Crypto fraud often emerges through misrepresentation, opaque governance, and incentive misalignment. Promises of outsized returns, unverifiable technical claims, and centralization of information signal risk. Case studies reveal inconsistent audits, custodial uncertainty, and regulatory gaps exploited by operators who control narratives. Protective measures emphasize transparency and independent verification. The pattern is persistent but inconsistencies and red flags vary by scheme, leaving stakeholders with crucial questions about integrity and oversight that demand closer scrutiny. The next steps lay out the concrete checkpoints investors should demand.
How Crypto Fraud Typically Unfolds
Crypto fraud typically unfolds through a combination of misrepresentation, manipulation of incentives, and opaque operations that obscure risk. In practice, schemes center on unverified token claims, custodial risk, and unclear whitepaper language that masks fundamentals.
Projects exploit vague disclosures, externalization of liability, and missing audits to project legitimacy while concealing vulnerability, steering investment away from verifiable safeguards toward opaque opportunities.
Red Flags That Predict a Scam
Red flags tend to cluster around claims that promise outsized returns with minimal risk, vague or unverifiable tech details, and operators who control information flow. In a detached assessment, the discourse catalogs red flags as fraud indicators rather than assurances, highlighting unrealistic returns, opaque governance, pressure to reinvest, and exit scams. Cautious scrutiny guards freedom and reduces exposure to manipulative schemes.
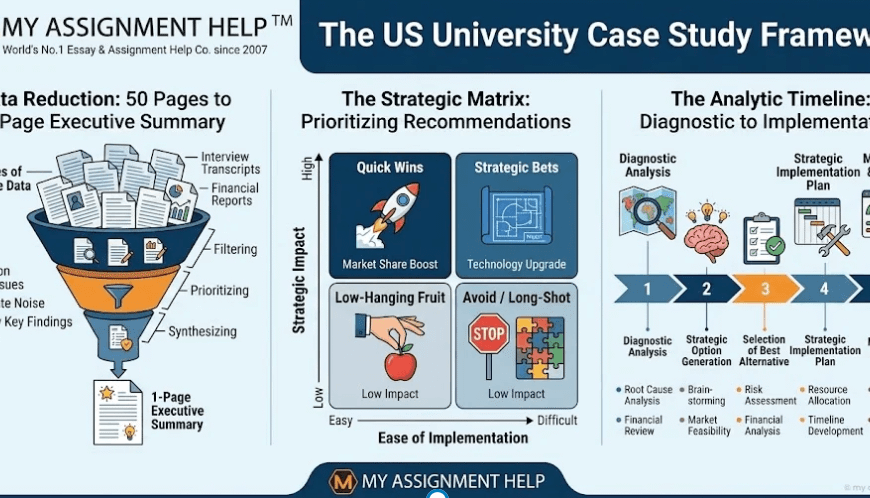
Case Studies: Lessons From Major Frauds
The examination of major frauds through concrete case studies demonstrates how initial red flags—such as promised outsized returns with little risk and opaque governance—often foreshadow systemic failures. Case analyses reveal patterns: misaligned incentives, opaque accounting, and regulatory gaps exploited before corrective measures emerged. Lessons emphasize innovation gaps, regulatory challenges, and disciplined due diligence for freedom-focused investors seeking transparent, evidence-based safeguards.
Protecting Your Portfolio: Practical Safeguards
Safeguarding a crypto portfolio requires a rigorous, evidence-based approach that prioritizes transparency, governance, and verifiable controls. Institutions emphasize documented procedures, incident drills, and independent audits to deter fraud.
Risk mitigation emphasizes defensive measures, strict access controls, and contingency planning.
A prudent diversification strategy reduces exposure concentration, while verified asset custody and transparent governance bolster resilience against deceptive schemes and operational failures.
See also: Financial Innovation Through Technology
Frequently Asked Questions
Can Regulators Truly Recover Stolen Crypto Funds in Scams?
Regulators cannot fully recover stolen crypto funds; limitations persist. The process facesRecovery obstacles due to cross-border, tracing challenges, exchange cooperation gaps, and legal constraints. Regulator limitations shape outcomes, demanding scrutiny, skepticism, and accountability within a freedom-oriented governance framework.
How Do Fraudsters Profit From Rug Pulls Beyond Hype?
Fraudsters profit from rug pulls by exploiting tokenomics manipulation and pump and dump dynamics, shifting value through sensational hype while draining liquidity; investigators must evaluate evidence, motives, and market observations, maintaining skepticism and upholding transparent, freedom-focused regulatory accountability.
What Are Common Data Sources for Confirming Fraud Claims?
Data sources include on-chain analytics, exchange transaction histories, smart contract audits, and legal filings; fraud verification relies on cross-referencing timelines, wallet clustering, and market-floor data, while maintaining skepticism and evidentiary standards for an audience seeking freedom.
Do Victims Have Legal Recourse After Crypto Losses?
Victims have limited legal recourse after crypto losses, though recourse avenues exist through civil claims, regulatory complaints, and criminal prosecutions. The assessment emphasizes victims’ rights, evidentiary hurdles, and skepticism toward promises of easy restitution.
How Does Cross-Border Enforcement Impact Case Outcomes?
Cross-border cooperation shapes outcomes; enforcement challenges persist. For example, a hypothetical investor case shows disparate legal standards affecting recovery, as authorities struggle with jurisdiction. Skeptically, the case illustrates limited remedy despite robust evidence and international cooperation requirements.
Conclusion
Crypto fraud typically thrives on misrepresentation, hidden risk, and opaque control. A disciplined, skeptical lens—demanding verifiable claims, independent audits, and custodian clarity—is essential. Consider the anecdote of a founder who touted “impossibly” high returns while controlling access to data and funds; the ensuing collapse mirrors a house of cards built on trust rather than verifiable standards. Data point: many losses spike after opaque whitepapers and centralized control are introduced. Conclusion: rigorous governance and transparency measurably reduce exposure to fraud.