Financial data security requires layered defenses, governance, and ongoing improvement to guard sensitive information from cyber threats, insider risk, and misconfigurations. Encryption, monitoring, and robust access controls reduce exposure for data at rest and in transit. Governance and identity programs address compliance and insider risk. A practical roadmap for detection, response, and resilience enables faster containment and informed risk-taking, while maintaining trust and value—an approach that invites further consideration of how to implement it effectively.
How Financial Data Is At Risk and Why It Matters
Financial data faces persistent exposure from cyber intrusions, insider breaches, and system misconfigurations, making protection not just a technical concern but a strategic business imperative.
The segment highlights how data leakage erodes trust and market value, while fraud analytics identify patterns—enabling timely intervention.
Awareness of threats empowers decisive controls, governance, and principled risk-taking to sustain freedom and resilience.
Build a Baseline: Core Defenses for Data at Rest and in Motion
A baseline of core defenses for data at rest and in motion is essential to reduce exposure and enable timely risk responses. The approach prioritizes layered controls, encryption, and monitoring to protect sensitive information while preserving agility. Data at rest protections deter unauthorized access; data in motion safeguards prevent interception. Strategic, concise measures align security with freedom and resilience.
Governance and Identity: Access, Compliance, and Insider Risk
Building on a baseline of data protections, this subtopic centers on who can reach data, under what conditions, and how activities are monitored and governed.
It examines identity governance frameworks, access controls, and policy alignment to regulatory expectations, while highlighting insider risk as a strategic concern.
The tone remains risk-aware, concise, and suitable for freedom-valuing audiences navigating governance complexities.
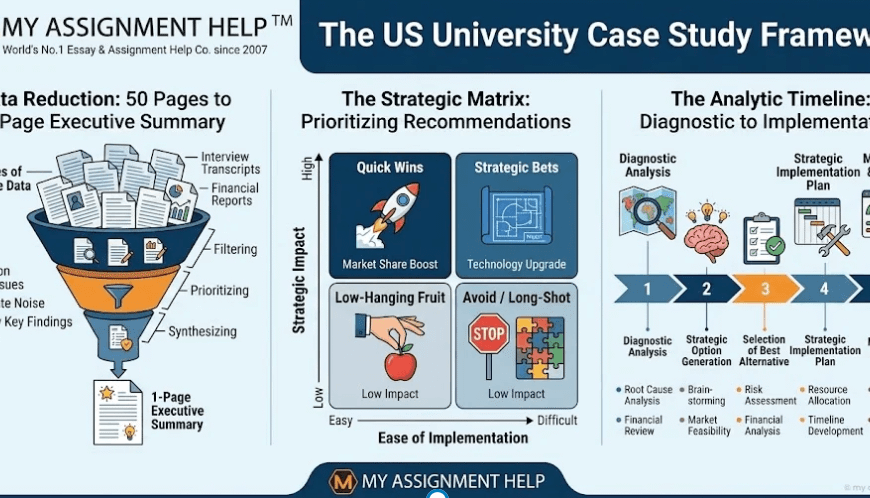
Practical Roadmap: Detection, Response, and Resilience Practices
The Practical Roadmap for detection, response, and resilience translates risk-aware principles into concrete, iterative workflows that organizations can implement now. It emphasizes proactive data provenance controls, streamlined incident triage, and measurable recovery objectives. Alert tuning calibrates signals to minimize noise while preserving vigilance, enabling rapid containment. This strategy champions disciplined governance, continuous improvement, and freedom to adapt defenses to evolving financial data threats.
See also: busyrush
Frequently Asked Questions
How Do Specific Regulatory Fines Impact Daily Security Budgeting Decisions?
Regulatory fines pressure organizations to reallocate resources toward compliance, shaping daily budgeting decisions. The risk-aware view notes fines act as a deterrent, prompting strategic investments, efficiency gains, and ongoing monitoring, while preserving autonomy and a freedom-minded security posture.
What Are the Hidden Costs of Data Breach Notifications?
Like a silent avalanche, the hidden costs of data breach notifications accumulate beyond alerts. They include breach notifications, privacy fines, and regulatory impact, shaping risk-aware budgeting; strategic decisions must balance transparency with costs, enabling freedom within compliance constraints.
How Can Small Firms Measure the True ROI of Security Investments?
ROI measurement challenges persist for small firms, as ROI remains elusive amid intangible security gains; budget tradeoffs complicate decisions, but strategic, risk-aware analysis enables smarter investments that preserve freedom while reducing exposure and incident costs.
Which Emerging Threats Most Affect Customer Trust and Retention?
A 72% spike in customer trust erosion accompanies zero-day exploits; emerging threats most affect loyalty. The analysis shows that vigilant risk management and transparent communication preserve customer trust, guiding strategic investments while maintaining freedom in security posture.
How Should Vendors Be Evaluated for Security Posture and Assurance?
Vendor due diligence and security metrics enable evaluators to assess posture through objective controls, third-party audits, and incident history; a risk-aware, strategic approach guides selection, balancing freedom-loving autonomy with assurance requirements and ongoing monitoring for sustained trust.
Conclusion
In sum, financial data security demands a layered, proactive posture that treats risk as a constant lens, not a momentary issue. The article emphasizes encryption, vigilant monitoring, and rigorous access governance as nonnegotiables, reinforced by a practical detection-and-response roadmap. By embedding governance into everyday operations, organizations illuminate weaknesses before they fracture trust. It’s a tightrope walk, but with disciplined controls and swift recovery plans, they can weather threats and keep stakeholder confidence intact. It’s not about if, but when. Stick to the plan.